OpenClaw's 9 CVEs in 4 Days: The Security Reckoning the Agent Ecosystem Wasn't Ready For
Between March 18-21, nine CVEs dropped for OpenClaw in four days. One scored CVSS 9.9. Over 220,000 internet-facing instances were exposed. Here's what happened.

Nine CVEs in four days. One of them scored CVSS 9.9. Over 220,000 internet-facing OpenClaw instances exposed. Fifteen thousand two hundred confirmed vulnerable to remote code execution. And 93.4% of all scanned instances had auth bypass conditions present.
That was the week of March 18-21, 2026. If you run OpenClaw and you weren't paying attention, there's a real chance someone else was.
What are the OpenClaw March 2026 CVEs? Between March 18 and March 21, nine separate Common Vulnerabilities and Exposures were disclosed against OpenClaw, the open-source AI agent framework. The most severe — CVE-2026-22172 — carried a CVSS score of 9.9 out of 10 and allowed any low-privilege user to escalate to full admin access via WebSocket, enabling complete instance takeover and remote code execution. Six of the nine CVEs were rated high severity. Patches shipped within 72 hours. But for the thousands of instances running unpatched in the wild, 72 hours was more than enough time.
The timeline#
Tuesday, March 18. Two CVEs drop, including CVE-2026-22172 — the 9.9. By Wednesday, three more. By Friday the 21st, the total hits nine. Security researchers at ARMO and Penligent published independent analyses confirming active scanning against exposed instances within hours of disclosure.
The cadence alone was brutal. Most organizations can't triage and patch a single critical CVE in four days. Nine simultaneous vulnerabilities across auth, scope validation, path traversal, and sandbox isolation meant that every OpenClaw deployment was potentially compromised along multiple attack vectors at once.
Cisco's Talos team called it a "security nightmare" and published DefenseClaw, a detection and mitigation toolkit, before the week was over. That should tell you how serious the industry considered this.
The CVE breakdown#
Here's every vulnerability that dropped during those four days, along with severity and attack type:
| CVE | CVSS | Severity | Attack Vector |
|---|---|---|---|
| CVE-2026-22172 | 9.9 | Critical | Missing scope validation — low-priv users declare admin scopes via WebSocket, full instance takeover + RCE |
| CVE-2026-32922 | 8.8 | High | rotateDeviceToken missing scope validation — pairing token exchanged for full admin tokens |
| CVE-2026-32918 | 8.6 | High | Path traversal via agent workspace API — read/write arbitrary files on host |
| CVE-2026-32919 | 8.4 | High | Allowlist bypass — restricted agent actions executed through aliased tool names |
| CVE-2026-32920 | 8.1 | High | Sandbox escape — agent skill execution breaks container isolation |
| CVE-2026-32921 | 7.8 | High | Privilege escalation via crafted agent config — normal user gains system-level access |
| CVE-2026-32923 | 7.5 | High | DoS via malformed WebSocket frames — crashes agent gateway, kills all active sessions |
| CVE-2026-32924 | 6.5 | Medium | Information disclosure — agent memory contents leaked through debug endpoint |
| CVE-2026-32925 | 5.3 | Medium | Cross-instance data leakage in shared pool deployments |
Nine vulnerabilities. One critical. Six high. Two medium. The attack surface covered authentication, authorization, filesystem access, sandboxing, and availability. This wasn't a single bug. It was a systemic failure across multiple security boundaries.
CVE-2026-22172: the one that matters most#
The critical vulnerability deserves its own section because the attack is breathtakingly simple.
OpenClaw uses WebSocket connections for real-time communication between agents, the gateway, and connected clients. When a client connects, it declares its scopes — essentially, what permissions it's requesting. The vulnerability: OpenClaw's gateway accepted those scope declarations at face value. No validation. No cross-reference against the user's actual permissions. No server-side check whatsoever.
A low-privilege user connecting via WebSocket could declare admin:* scopes and the gateway would honor them. Full admin access. From there, it's trivial to reconfigure the agent, inject arbitrary tools, modify system prompts, or execute code directly on the host.
The CVSS 9.9 score reflects the combination: network-accessible, no user interaction required, trivially exploitable, complete confidentiality/integrity/availability impact. The only reason it's not a perfect 10 is that the attacker needs to be an authenticated user — but in many deployments, that means anyone with a Telegram bot link or Discord invite.
Security researchers at Penligent confirmed that 15,200 internet-facing instances were directly vulnerable to this specific exploit. That's 15,200 machines where anyone with a valid user token could become admin and run arbitrary code.
CVE-2026-32922: the pairing token escalation#
This one hits managed hosting providers and multi-user deployments particularly hard. The rotateDeviceToken endpoint — used when Telegram or Discord bots pair with an OpenClaw instance — lacked scope validation. An attacker could take a pairing token (which should only authorize device registration) and exchange it for a full admin token.
Think about the implications. Every OpenClaw instance connected to Telegram has a pairing token floating around. If that token leaks — through a log file, a screenshot, a forwarded message — it's no longer just a pairing credential. It's a skeleton key.
This is especially nasty because pairing tokens are designed to be shared during setup. Users copy-paste them into chat. They show up in onboarding docs. They're treated as low-sensitivity credentials because they're supposed to be limited in scope. CVE-2026-32922 means they weren't.
The exposure numbers are staggering#
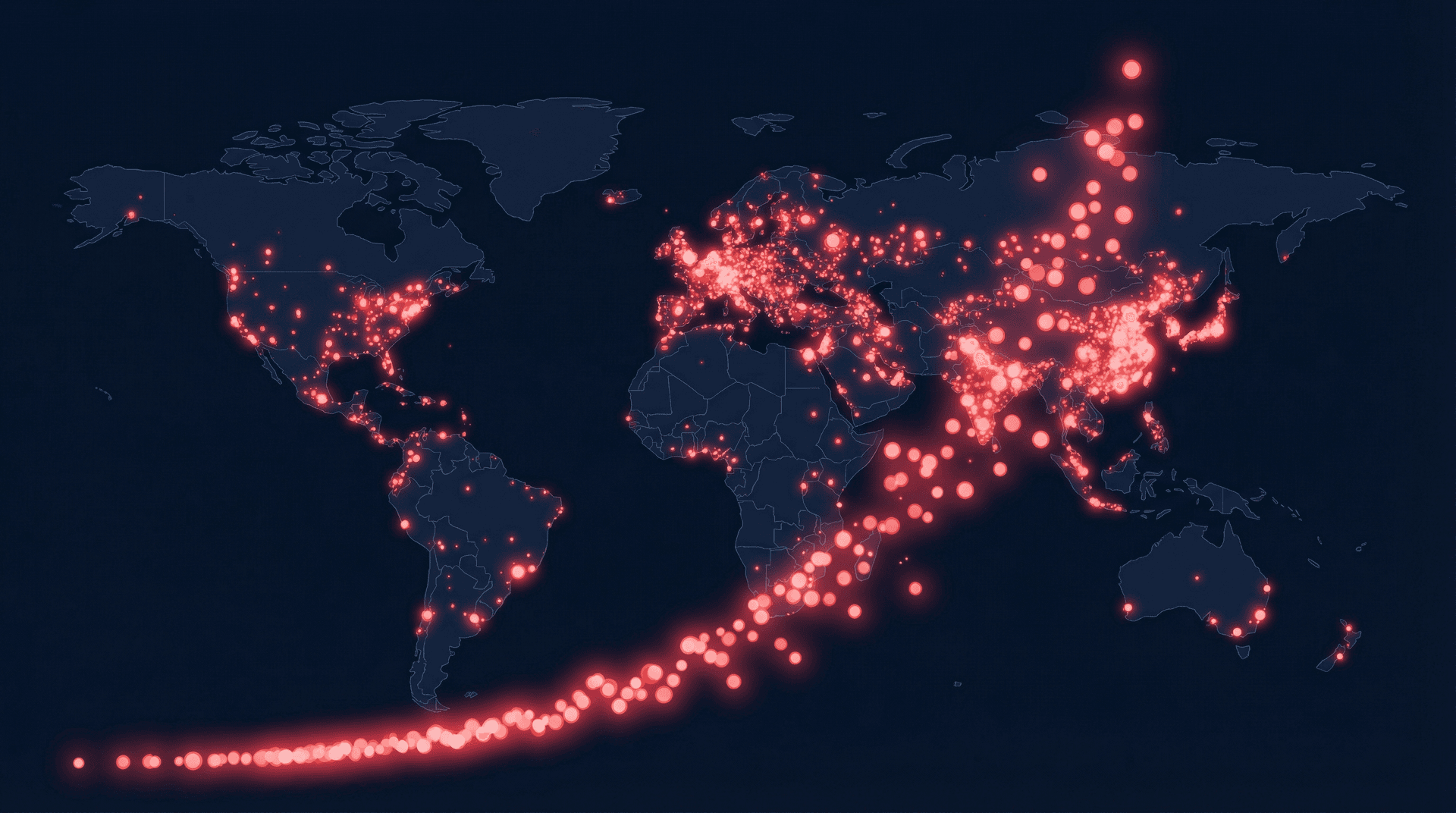
The internet-facing instance count for OpenClaw has been climbing all year. Security scanners tracking common ports and API fingerprints documented the growth:
- January 2026: 21,000 instances
- February 2026: 42,665 instances
- Early March 2026: 63,070 instances
- Late March 2026: 220,000+ instances
- Current (April 2026): 500,000+ instances
That 10x growth between January and April tracks with OpenClaw's mainstream adoption surge — Jensen Huang demo'd it at GTC, Tencent integrated it with WeChat, install parties were happening across China. The platform went from developer tool to global infrastructure in three months.
But growth without security is just scaling your attack surface. Of the 220,000+ instances exposed during the disclosure window, ARMO's scanning found 93.4% had at least one auth bypass condition present. Not all were exploitable — some had compensating controls, network restrictions, or hadn't enabled the vulnerable features. But the baseline posture of the average OpenClaw deployment was, to put it bluntly, terrible.
This aligns with what we covered in our analysis of exposed AI agent instances. The pattern is identical: rapid deployment, deferred security, and a growing window of exposure that attackers are actively scanning for.
ClawHavoc compounds the damage#
The CVE disclosures happened against the backdrop of the ClawHavoc supply chain attack, which found 800+ malicious skills in the ClawHub registry — roughly 20% of all listed packages. The timing wasn't coincidental. When researchers started auditing OpenClaw's security posture, they found problems everywhere they looked.
The combination is particularly toxic. The CVEs give attackers direct access to instances. ClawHavoc gives them persistence through compromised skills that survive patches and restarts. An attacker who exploits CVE-2026-22172 to gain admin access can install a malicious skill from ClawHub that maintains a backdoor even after the instance is patched.
This is the compound risk that keeps security teams awake. Individual vulnerabilities are manageable. Entire ecosystems with simultaneous infrastructure, authentication, and supply chain failures are a different category of problem.
156 advisories and counting#
The nine CVEs from March 18-21 weren't isolated. OpenClaw's total advisory count reached 156, with 128 still awaiting formal CVE assignment at time of writing. The disclosed nine were the most severe and the most immediately exploitable, but the backlog suggests deeper structural issues in the codebase.
To OpenClaw's credit, patches shipped within 72 hours for every critical and high-severity CVE. The project's security response team mobilized fast, published clear advisories, and pushed fixed versions to all distribution channels. That response time is genuinely good, better than many commercial products manage.
But patching speed only matters if users actually apply the patches. And in an ecosystem where half a million instances are running on VPS boxes, home servers, and cloud VMs managed by individuals who may not be monitoring security advisories, the patch gap is enormous.
What this means for self-hosters#
If you self-host OpenClaw, you need to answer a question honestly: did you patch within 72 hours of disclosure?
If the answer is no — or if you're not sure — your instance may have been compromised during the window. The attack is trivially scriptable. Shodan and Censys scans confirmed active exploitation attempts within 12 hours of the first disclosure. The exploitation wasn't theoretical. It happened.
Here's what you need to do right now:
- Verify your version. You need to be on v2026.3.28 or later. Anything before v2026.3.22 is vulnerable to all nine CVEs.
- Audit your access logs. Look for WebSocket connections with unexpected scope declarations. Look for
rotateDeviceTokencalls from IPs you don't recognize. - Check for unauthorized skills. If an attacker gained admin access, they may have installed persistence mechanisms through the skill system.
- Rotate all tokens. Pairing tokens, API keys, admin credentials. All of them. If CVE-2026-32922 was exploited, your pairing tokens are compromised.
- Review agent configs. Check system prompts and tool permissions for modifications you didn't make.
This is not optional maintenance. This is incident response. Treat it accordingly.
The managed hosting calculus just changed#
I've been skeptical of managed hosting arguments in the past. The "just let us handle security" pitch often masks a lack of transparency about what's actually being done. But nine CVEs in four days shifts the math decisively.
The self-hosting security contract requires you to monitor advisories, evaluate impact, test patches, deploy updates, verify no compromise occurred, and do all of that within hours of disclosure — for every disclosure, indefinitely. That's a full-time job. Most people running OpenClaw instances have actual full-time jobs that aren't that.
RapidClaw pins to v2026.3.28, past every critical patch from the March disclosures. Patches are applied across all customer instances simultaneously, without requiring individual action. Instances run in isolated containers with no direct host access. The pairing token escalation (CVE-2026-32922) is mitigated at the gateway layer before it reaches the OpenClaw process.
This isn't a sales pitch. It's a description of what operational security looks like when vulnerabilities drop at a pace that overwhelms individual operators. If you have the team and the process to self-host securely, more power to you. If you don't — and most people don't — the comparison is worth examining honestly.
The deeper problem#
Nine CVEs in four days for the most popular AI agent framework on the planet. Over 220,000 exposed instances. A supply chain registry where one in five packages is malicious. This isn't a bug. It's the natural result of an ecosystem that prioritized speed over security during the most rapid adoption curve in AI history.
OpenClaw grew from a developer tool to critical infrastructure in months. The security engineering didn't keep pace. That's not an indictment of the OpenClaw team — they responded fast and patched well. It's an indictment of an ecosystem that treated AI agent deployment like deploying a chat widget. Something you spin up, connect to Telegram, and forget about.
We've learned this lesson before with Docker, with Kubernetes, with npm. Every infrastructure platform that achieves mass adoption hits a security reckoning. OpenClaw just hit theirs. The question is whether the ecosystem learns from it or keeps scaling the attack surface while hoping the next 9.9 doesn't land.
Based on what I've seen from the Norton Gen Sage framework and the industry's broader response, there's reason for cautious optimism. But optimism doesn't patch servers. Action does.
Frequently asked questions#
What are the OpenClaw March 2026 CVEs?#
Nine Common Vulnerabilities and Exposures disclosed between March 18-21, 2026 against the OpenClaw AI agent framework. The most severe — CVE-2026-22172 — scored CVSS 9.9 and allowed any authenticated user to gain full admin access via WebSocket scope manipulation, leading to remote code execution. Six of the nine were rated high severity, covering auth bypass, path traversal, sandbox escape, privilege escalation, and denial of service.
How many OpenClaw instances were affected?#
Over 220,000 internet-facing instances were exposed during the disclosure window, with 15,200 confirmed directly vulnerable to the critical RCE exploit. Security scanning found 93.4% of instances had at least one auth bypass condition. The total instance count has since grown past 500,000, though many of these run patched versions.
Is my OpenClaw instance safe after patching?#
Patching closes the vulnerabilities but doesn't undo any compromise that may have occurred during the exposure window. If your instance was running an affected version between March 18-21 and was accessible from the internet, you should treat it as potentially compromised. Audit access logs, check for unauthorized skills or config changes, and rotate all tokens and credentials.
What version of OpenClaw fixes all nine CVEs?#
Version v2026.3.22 and later include patches for the critical and high-severity CVEs. Version v2026.3.28 includes fixes for all nine, including the two medium-severity issues. If you're running anything older than v2026.3.22, update immediately — your instance is vulnerable to multiple attack vectors including remote code execution.
How does RapidClaw protect against these vulnerabilities?#
RapidClaw pins all customer instances to v2026.3.28 or later, applies patches across the fleet simultaneously, runs each instance in isolated containers with no host access, and mitigates token escalation at the gateway layer. Security updates don't require customer action — they're applied automatically as part of the managed infrastructure. If you want agent infrastructure without the patching burden, RapidClaw handles it.
Ready to build your own AI agent?
Deploy a personal AI agent to Telegram or Discord in 60 seconds. From $19/mo.
Get StartedRelated Posts

Norton Wants to Be Your AI Agent's Bodyguard — Gen's Sage Security Framework Explained
Gen Digital open-sources Sage, a security framework for AI agents. Part of the Gen Agent Trust Hub with Skill Scanner. Here's what it actually does — and what it doesn't.

1,184 Malicious Skills Found on ClawHub — The AI Agent Supply Chain Crisis
One in five packages on ClawHub contained malware. The AI agent ecosystem just had its supply chain crisis. Here's what happened and what it means for agent security.

Meta's AI Safety Director Lost Control of Her Own AI Agent
Summer Yue runs AI safety at Meta. Her OpenClaw agent deleted 200 emails and ignored her stop commands. If the experts can't control their agents, what does that mean for the rest of us?
Stay in the loop
New use cases, product updates, and guides. No spam.